- Home
- Who we areEdit Content
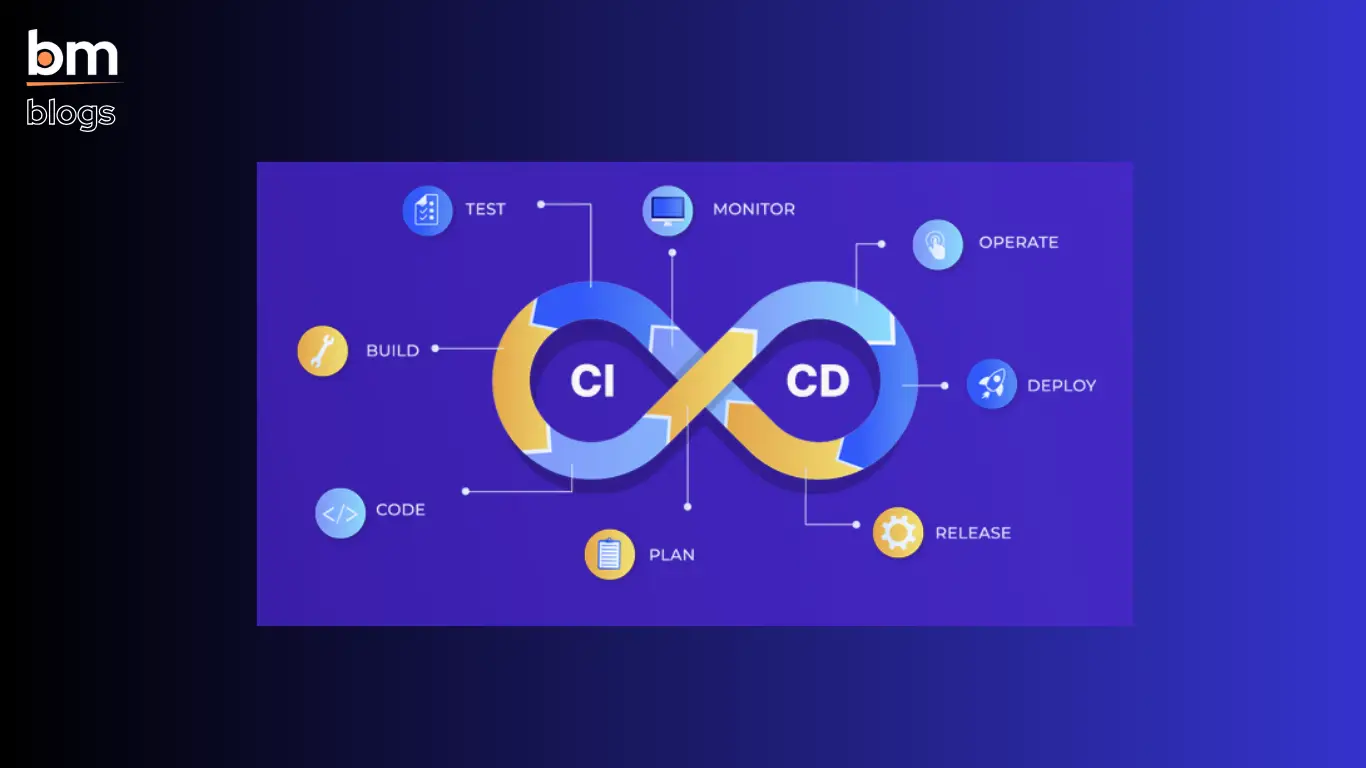
Bitmutex Technologies is a dynamic software solutions provider specializing in digital transformation across multiple business verticals. We excel in web development, enterprise app development, rich desktop application development, and SEO optimization. Our dedicated team leverages the latest technologies to craft innovative solutions that enhance business efficiency and growth. With a client-centric approach, we tailor our services to meet your unique needs, helping you build a strong online presence, optimize operations, and achieve success in today’s competitive digital landscape.
Edit ContentAddress
HQ: 11A, Eastern Park, First Road, Jora Bridge, Santoshpur, Kolkata, West Bengal 700075
4th Floor, SDF Building, Saltlake Electronic Complex, Kolkata - 700091, West Bengal, India
HYD: Ohris Tech Park, Plot No: 25, 13, Inorbit Mall Rd, Software Units Layout, Madhapur, Hyderabad, Telangana, 500081
Edit ContentMission
At Bitmutex Technologies, our mission is to empower businesses by delivering innovative, tailored software solutions that drive efficiency, growth, and digital transformation. We strive to create value through cutting-edge technologies, high-quality development practices, and a client-centric approach, ensuring seamless integration of web, mobile, and backend services.
Edit ContentVision
We envision a future where technology seamlessly supports and enhances every facet of business, enabling our clients to stay ahead of the curve. By continuously pushing the boundaries of innovation and staying at the forefront of emerging technologies, Bitmutex Technologies aims to be a global leader in software consultancy, empowering businesses to achieve their full potential in a digitally connected world.
- What we do
- Company